Tricks and Tips to Crack Password
Different techniques of hacking and cracking the unknown password and having fun with it.

Most Passwords can be Cracked by using following Techniques :
1) Hashing
One example is the LM Hash that Microsoft Windows uses by Default to Store User Passwords that are Less than 15 Characters in Length. LM Hash Breaks the Password into two 7 character fields which are then hashed separately allowing each half to be attacked separately. Hash functions like SHA-512, SHA-1 and MD5 are considered Impossible to Invert when used Correctly.
2) Guessing
Examples of insecure choices include:
- blank (none).
- the word “password”, “passcode”, “admin” and their Derivatives.
- the User’s Name or Login Name.
- the Name of their significant other or another person (loved one).
- their Birthplace or Date of Birth.
- a Pet’s Name.
- a Dictionary Word in any Language.
- Automobile Licence Plate Number.
- a row of letters from a Standard Keyboard Layout (eg. asdf or qwertyuiop).
- a simple Modification of one of the Preceding, such as Suffixing a digit or Reversing the order of the letters.
So it is quite easy for an Attacker to Enter Default Password and gain Access to Sensitive Information. A list containing Default passwords of some of the most Popular Applications is available on the Internet. Always Disable or Change the Applications (both online and offline) Default Username Password Pairs.
4) Brute Force
As soon as Correct Password is reached it Displays on the Screen. This Techniques takes extremely Long Time to Complete, but Password will surely Cracked. Long the Password is, Large is the Time taken to Brute Force it.
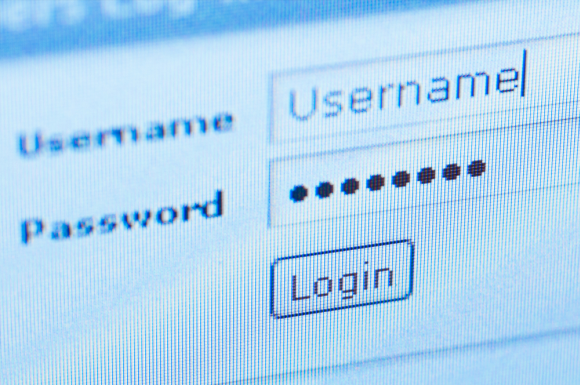
5) Phishing

Phishing is a Technique in which the Attacker Creates the Fake Login Screen and send it to the Victim hoping that the Victim gets Fooled into Entering the Account's Username and Password. As soon as Victim Login, the Information reaches to the Attacker using Scripts or Online form Processors while the Victim is Redirected to Home Page of Email Service Provider. Never give reply to the Messages which are demanding for the Username or Password.
It is also possible to obtain the Passwords through other different methods such as Social Engineering, Wiretapping, Keystroke Logging, Login Spoofing, Dumpster Diving, Phishing, Shoulder Surfing, Timing Attack, Acoustic Crypt analysis using a Trojan Horse or Virus, Identity Management System Attacks, Compromising Host Security, etc.
So these are simple Tricks and tips to crack password.